Introduction:
In the digital era, online businesses rely on secure and efficient payment gateways to facilitate transactions and ensure smooth financial operations. Numerous payment gateways are available in the market, each offering its own set of features and advantages. In this article, we will explore and compare eleven popular payment gateways, including Paypal, 2CheckOut, Stripe, WorldPay, GooglePay, ApplePay, AliPay, WePay, Skrill, BrainTree, and Adyen. By examining their pros and cons, we aim to help businesses make informed decisions when selecting the most suitable payment gateway for their online ventures.

1. Paypal:
Paypal is one of the most widely recognized and trusted payment gateways globally. It allows businesses and individuals to send and receive payments securely online.
Pros:
- Brand Recognition: Paypal enjoys widespread recognition and trust among consumers, which can increase conversion rates.
- User-Friendly Interface: Paypal offers a simple and intuitive interface, making it easy for businesses and customers to navigate the payment process.
- Global Reach: Paypal supports transactions in multiple currencies, allowing businesses to cater to international customers.
Cons:
- Transaction Fees: Paypal charges transaction fees, which can be relatively higher compared to some other payment gateways.
- Limited Customization: Paypal's checkout process and appearance are standardized, providing limited flexibility for businesses to match their brand identity.
- Account Holds: Paypal has a reputation for placing holds on funds in certain cases, which can be inconvenient for businesses.
2. 2CheckOut:
2CheckOut is a payment gateway that enables businesses to accept online payments from customers worldwide.
Pros:
- Global Reach: 2CheckOut supports transactions in multiple currencies and offers localized payment options, allowing businesses to expand their international reach.
- Secure and Reliable: 2CheckOut employs robust fraud protection measures and secure payment processing, ensuring safe transactions for businesses and customers.
- Easy Integration: 2CheckOut provides user-friendly integration options with popular e-commerce platforms and APIs.
Cons:
- Limited Payment Methods: 2CheckOut's available payment methods may be more limited compared to some other payment gateways, which could potentially affect conversion rates.
- Transaction Fees: 2CheckOut charges transaction fees, which may vary depending on the business's location and the payment method used.
- Support Availability: Some users have reported challenges in obtaining timely and responsive support from 2CheckOut.
3. Stripe:
Stripe is a versatile payment gateway that offers a developer-friendly platform, allowing businesses to integrate and customize payment processing in their applications.
Pros:
- Developer-Focused: Stripe provides extensive documentation, APIs, and libraries, making it a popular choice for businesses with specific customization requirements.
- Transparent Pricing: Stripe offers straightforward pricing with no setup fees, monthly fees, or hidden costs. Transaction fees vary based on the business's location and payment method.
- International Support: Stripe supports transactions in multiple currencies and offers localized payment options, enabling global expansion.
Cons:
- Account Stability: Stripe's risk management measures can sometimes result in account holds or suspensions, which may cause disruptions for businesses.
- Integration Complexity: While Stripe offers powerful customization options, integrating and configuring the payment gateway may require technical expertise.
- Limited Customer Support: Some users have reported challenges in accessing timely and responsive customer support from Stripe.
4. WorldPay:
WorldPay is a leading global payment gateway that provides a range of payment solutions for businesses of all sizes.
Pros:
- Extensive Payment Methods: WorldPay supports a wide array of payment methods, including credit cards, e-wallets, and alternative payment options, catering to diverse customer preferences.
- Multi-Currency Support: WorldPay enables businesses to accept payments in multiple currencies, facilitating international transactions.
- Advanced Fraud
Prevention: WorldPay offers robust fraud prevention tools and risk management features to protect businesses from fraudulent activities.
Cons:
- Pricing Complexity: WorldPay's pricing structure can be complex, with various fees and additional charges based on the business's specific requirements and transaction volumes.
- Contractual Obligations: WorldPay often requires businesses to enter into long-term contracts, which may limit flexibility and make it challenging to switch providers if necessary.
- Support Limitations: Some users have reported difficulties in obtaining responsive and helpful customer support from WorldPay.
5. GooglePay:
GooglePay is a digital wallet and payment gateway offered by Google, allowing users to make payments using their saved cards and enabling businesses to accept online payments.
Pros:
- Ease of Use: GooglePay offers a seamless and convenient payment experience for users, leveraging their existing Google accounts.
- Fast Checkout: GooglePay facilitates quick checkout experiences, reducing cart abandonment rates and improving conversions.
- Enhanced Security: GooglePay employs advanced security measures, including tokenization, to protect user data and transactions.
Cons:
- Limited Availability: GooglePay may have limited availability in certain regions, which could restrict its usage for businesses targeting specific markets.
- Integration Complexity: Integrating GooglePay into an existing e-commerce platform or website may require technical expertise or reliance on third-party plugins.
- Transaction Limits: GooglePay may have transaction limits, which businesses need to consider for high-value transactions.
6. ApplePay:
ApplePay is a mobile payment and digital wallet solution provided by Apple, allowing users to make payments using their Apple devices.
Pros:
- Seamless User Experience: ApplePay offers a convenient and frictionless payment experience for users with Apple devices, utilizing biometric authentication (Touch ID or Face ID) for added security.
- Brand Trust: ApplePay benefits from the strong brand reputation and trust associated with Apple products and services.
- Increased Conversions: The streamlined checkout process and user-friendly interface of ApplePay can contribute to improved conversion rates for businesses.
Cons:
- Limited Device Compatibility: ApplePay is exclusive to Apple devices, potentially excluding a significant portion of users who prefer other platforms.
- Integration Complexity: Integrating ApplePay into an e-commerce platform or website may require specific technical skills and knowledge of Apple's development guidelines.
- Restricted Access: ApplePay's availability may be limited to certain countries and regions, limiting its usability for businesses targeting global audiences.
7. AliPay:
AliPay, operated by Alibaba Group, is a widely used digital wallet and payment gateway in China, providing seamless online and offline payment solutions.
Pros:
- Dominant Market Presence: AliPay holds a significant market share in China, making it an essential payment gateway for businesses targeting the Chinese market.
- Wide User Adoption: AliPay is widely adopted by Chinese consumers, allowing businesses to tap into a large customer base.
- Integrated Ecosystem: AliPay offers additional features and services beyond payment processing, such as digital wallets, money transfers, and financial management tools.
Cons:
- Geographic Limitations: AliPay's prominence is primarily limited to China, making it less relevant for businesses targeting international customers.
- Compliance Requirements: Businesses seeking to accept AliPay may need to comply with specific regulations and requirements imposed by Chinese authorities.
- Integration Challenges: Integrating AliPay into non-Chinese e-commerce platforms or websites may involve technical complexities and additional considerations.
8. WePay:
WePay is a payment gateway that provides customizable payment solutions for online platforms, marketplaces, and crowdfunding platforms.
Pros:
- Platform-Focused: WePay specializes in catering to online platforms and marketplaces, offering tailored payment solutions for businesses operating in those domains.
- Easy Integration: WePay provides well-documented APIs and developer tools, facilitating seamless integration with various platforms and applications.
- Risk Management: WePay offers robust fraud detection and prevention measures, reducing the risk of fraudulent transactions for businesses.
Cons:
- Limited Business Types: WePay's primary focus on platforms and marketplaces may limit its suitability for businesses operating outside those categories.
- Restricted Accessibility: WePay's availability may be limited to certain countries or regions, potentially excluding businesses targeting global markets.
- Customer Support: Some users have reported challenges in obtaining responsive and satisfactory customer support from WePay.
9. Skrill:
Skrill is a digital wallet and payment gateway that enables businesses and individuals to send and receive payments globally.
Pros:
- Global Reach: Skrill supports transactions in multiple currencies, allowing businesses to operate in diverse international markets.
- Multiple Payment Methods: Skrill offers a wide range of payment options, including credit cards, bank transfers, and e-wallets, providing flexibility for businesses and customers.
- Enhanced Security: Skrill utilizes advanced security measures, including two-factor authentication and encryption, to protect user data and transactions.
Cons:
- Transaction Fees: Skrill charges transaction fees, which can vary depending on factors such as the payment method, currency conversion, and transaction volume.
- Withdrawal Restrictions: Skrill imposes certain limitations on withdrawal amounts and frequency, which may inconvenience businesses with specific cash flow requirements.
- Customer Support: Some users have reported challenges in receiving timely and satisfactory customer support from Skrill.
10. BrainTree:
BrainTree, owned by PayPal, is a full-stack payment platform that offers businesses a wide range of payment options and features.
Pros:
- Comprehensive Payment Solutions: BrainTree provides businesses with various payment methods, including credit cards, digital wallets, and alternative payment options, all integrated into a single platform.
- Developer-Friendly: BrainTree offers well-documented APIs and developer tools, allowing businesses to customize and integrate payment processing into their applications.
- Fraud Protection: BrainTree incorporates advanced fraud detection and prevention mechanisms to safeguard businesses from fraudulent transactions.
Cons:
- Complexity for Small Businesses: BrainTree's extensive feature set and customization options may be overwhelming for smaller businesses with limited technical resources.
- Transaction Fees: BrainTree charges transaction fees, which can vary based on the business's location, transaction volume, and the payment method used.
- Customer Support: Some users have reported challenges in obtaining responsive and satisfactory customer support from BrainTree.
11. Adyen:
Adyen is a global payment gateway that provides businesses with a unified platform to accept payments across multiple channels and countries.
Pros:
- Global Expansion: Adyen supports transactions in numerous currencies and provides localized payment options, enabling businesses to expand their operations globally.
- Omni-Channel Capabilities: Adyen facilitates payments across various channels, including online, mobile, in-store, and in-app, offering a seamless and consistent payment experience.
- Advanced Reporting and Analytics: Adyen provides comprehensive reporting and analytics tools, allowing businesses to gain insights into their transactions and customer behavior.
Cons:
- Pricing Structure: Adyen's pricing structure can be complex, with various fees and charges that may vary based on the business's specific requirements and transaction volumes.
- Onboarding Process: Some users have reported a lengthy onboarding process and strict underwriting requirements when setting up an account with Adyen.
- Support Availability: While Adyen offers customer support, some users have reported challenges in receiving prompt and satisfactory assistance.
Conclusion:
Selecting the right payment gateway is a crucial decision for online businesses. Paypal, 2CheckOut, Stripe, WorldPay, GooglePay, ApplePay, AliPay, WePay, Skrill, BrainTree, and Adyen are among the popular payment gateways available today, each offering distinct features, advantages, and limitations. Businesses must consider factors such as global reach, ease of integration, transaction fees, security measures, customer support, and compatibility with their target markets and platforms. By carefully evaluating the pros and cons of these payment gateways, businesses can make informed decisions and choose the most suitable solution to streamline their payment processes, enhance user experience, and drive business growth.










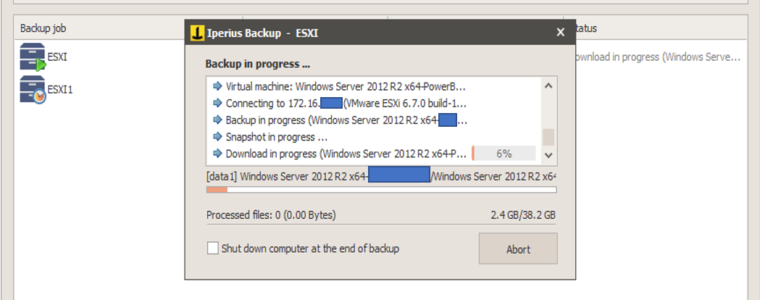
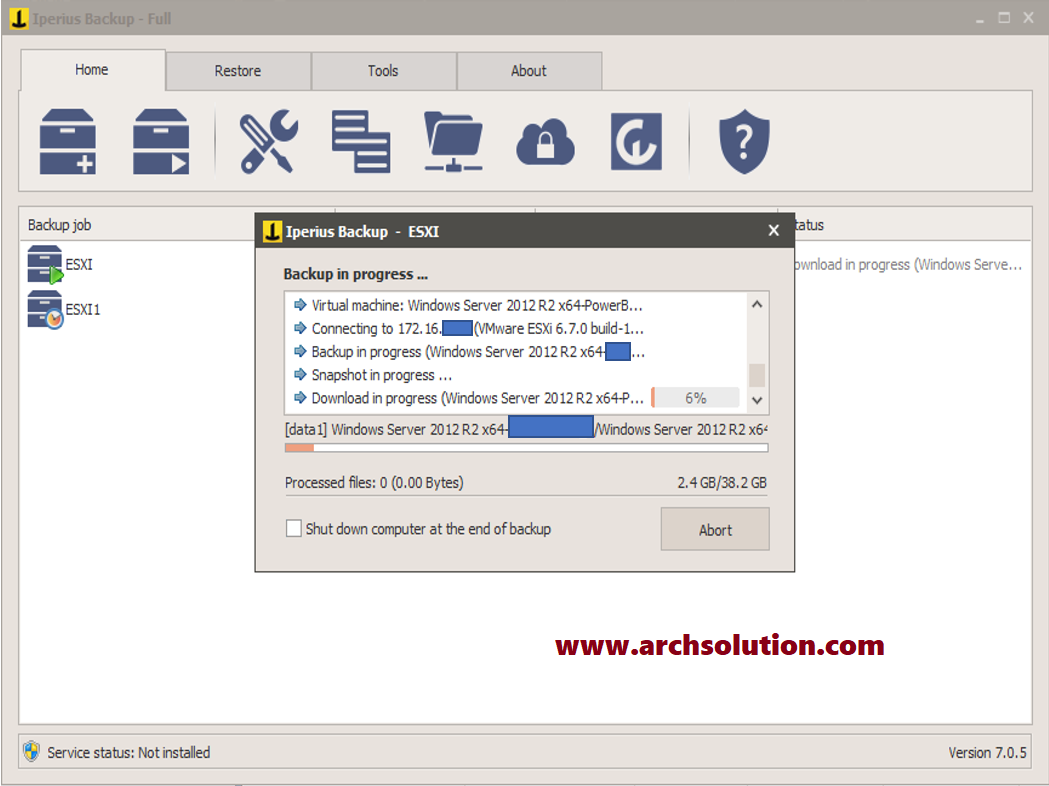 The most significant features of Iperius for this kind of backup are being list below:
The most significant features of Iperius for this kind of backup are being list below:
 Notes:
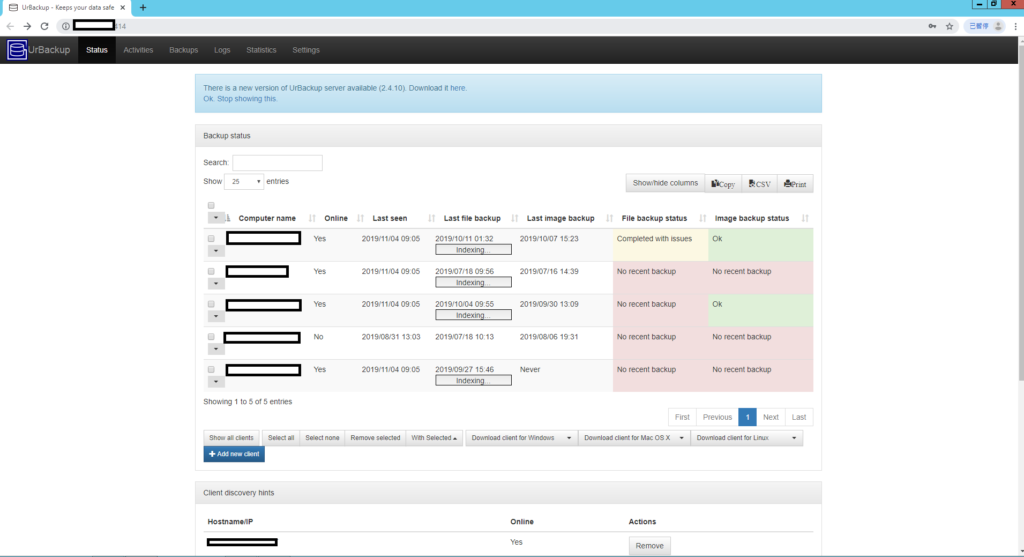
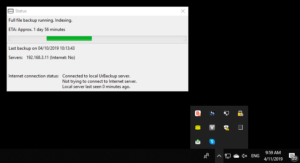
There are 3 different colours of the “Urbackup” client icon.
Notes:
There are 3 different colours of the “Urbackup” client icon.